Introduction
"Zero-day" is a broad term that describes recently discovered security flaws that hackers can use to attack systems. A zero-day attack is an attack in which a vulnerability is exploited before a fix is available or widely deployed. These attacks can be particularly damaging because traditional cyber defense strategies are ineffective in protecting against them. Many of these strategies rely on signature-based detection, which only works if the malware's signature is publicly available.
Keywords
- A zero-day vulnerability is a software vulnerability that is discovered by an attacker before the vendor is aware of it. Vendors are unaware of this, so there are no patches for zero-day vulnerabilities, making attacks more likely to succeed.
- A zero-day exploit is a method used by hackers to attack systems with previously unidentified vulnerabilities.
- A zero-day attack is the use of a zero-day exploit to corrupt or steals data from a system compromised by a vulnerability.
How do Zero-Day Attack Works
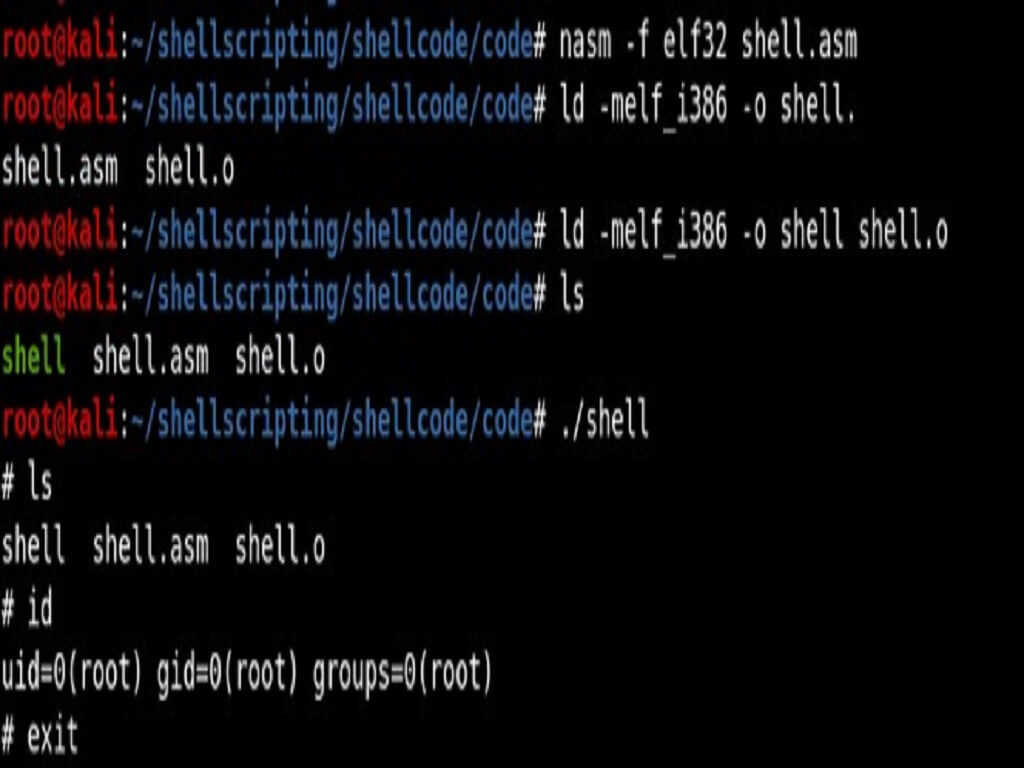
Sometimes hackers or malicious actors discover a vulnerability before software developers do. While the vulnerability is still open, attackers can create and implement code to exploit it. This is known as exploit code.
When vulnerabilities become known, developers try to patch them to stop attacks. However, security vulnerabilities are often not detected immediately. Sometimes it can take days, weeks, or even months for developers to identify the vulnerability that led to the attack. And even when a zero-day patch is released, not all users are quick to implement it. In recent years, hackers have been quicker to exploit vulnerabilities soon after they are discovered.
Exploits can sell for a lot of money on the dark web. Once an exploit is discovered and patched, it is no longer labeled as a zero-day threat.
Who carries out Zero-day attacks?
Malicious actors performing zero-day attacks fall into different categories depending on their motivation.
For example:
- Cybercriminals are people who use digital technology such as computers and the internet to carry out illegal activities.
- Hacktivists Hackers motivated by a political or social cause who want attacks to be visible to get attention for their cause.
- Corporate espionage Attackers who spy on companies to obtain information about them.
- Cyber warfare countries or political actors spying on or attacking another country's cyber infrastructure.
Who are the targets for Zero-Day attacks?
Zero-day hacks can exploit various system vulnerabilities,
- Operating system
- Internet browsers
- Office applications
- Open-source components
- Hardware and firmware
- Internet of Things (IoT)
How to identify Zero-Day attacks

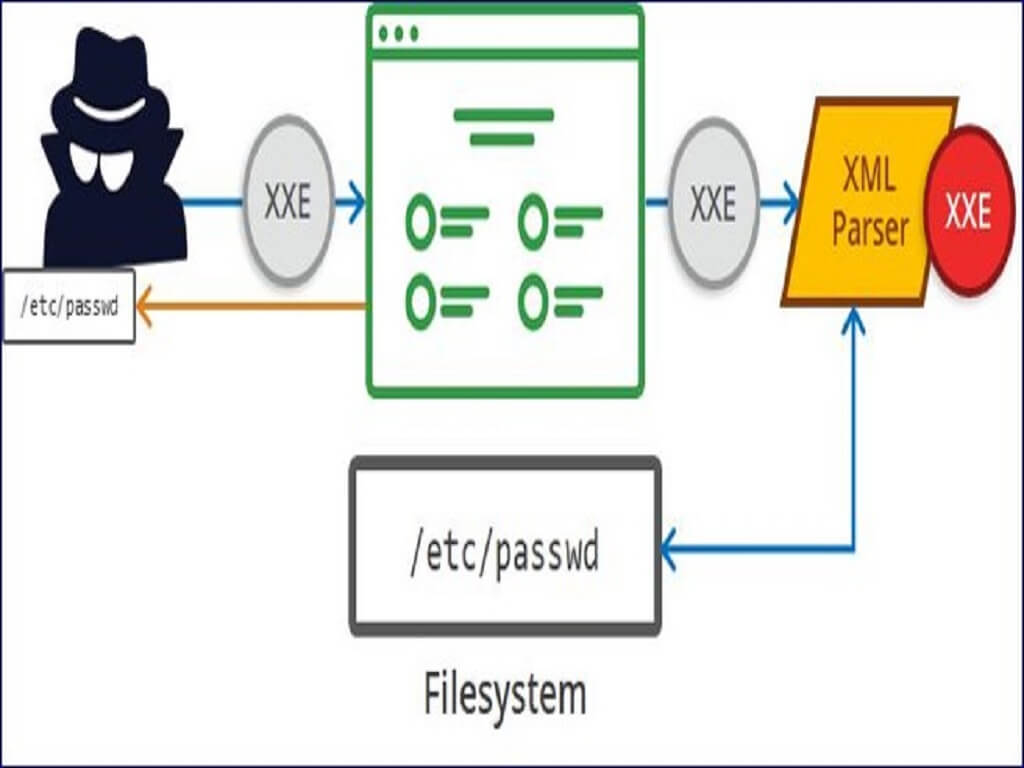
Attackers use zero-day exploits in a variety of ways:
- Spear phishing emails attached to files (example, Microsoft Office documents, Adobe PDFs, or other executable files or components) embedded in a zero-day exploit
- Phishing and spam emails are socially designed to lure unwitting recipients into clicking on URLs and links to malicious or compromised websites hosting an exploit (hole-filling attack)
- Exploit kits whose attack chains include malware and malicious websites that host zero-day exploits
- Compromising a system, server, or network – whether through brute force and dictionary attacks, misconfiguration, or inadvertent Internet exposure – where attackers can then use exploit malware.
Illustration of Zero-Day attack
Some recent examples of zero-day attacks include:
1) 2021: Chrome zero-day vulnerability
Google issued several zero-day threats to Chrome in 2021, which prompted Chrome to provide patches. A flaw in the web browser's V8 JavaScript engine led to this vulnerability.
2) 2020: Zoom
A security vulnerability has been found in the popular video conferencing platform. In this illustration of a zero-day assault, users' computers were remotely accessed by hackers if they were running an earlier version of Windows. A hacker might entirely take control of the victim's computer and acquire access to all of their files if the administrator was the target.
How to protect yourself against Zero-Day attacks
For zero-day protection and to keep your computer and data safe, it's essential that individuals and organizations follow cybersecurity best practices. It includes:
Keep all software programs and work structures updated.
This is because vendors include security patches that cover newly identified vulnerabilities in new releases. Keeping your information up-to-date ensures greater security.
Use only necessary applications.
The extra software you have, the extra vulnerabilities you have. Reduce risk to your network by using only the applications you need.
Use a firewall.
A firewall plays a vital role in protecting your system from zero-day threats. Ensure maximum protection by configuring to allow only necessary transactions.
Educate users within organizations.
Many zero-day attacks exploit human error. Teaching employees and users the right safety and security habits will help keep them safe online and protect organizations from zero-day exploits and other digital threats.
Use a complete antivirus software program.
By eliminating both known and undiscovered threats, antivirus software aids in keeping your device secure.
Conclusion
Zero-day exploits and attacks are modern threats that can affect any business, organization, and enterprise. They are often able to attack modern infrastructure. Everything the network processes is vulnerable to attack. Some forms of zero-day exploit malware have been developed by sophisticated parties, such as the Stuxnet virus (dangerous enough to be classified as a cyber-weapon).