What is a USB Drop Attack?
A USB drop attack occurs when an attacker strategically places a USB device somewhere, potentially containing malicious code, with the intention of someone taking it and plugging it into a computer. This type of attack employs the use of social engineering. Social Engineering, in terms of cyber security, is using deceptive means to manipulate individuals into divulging information or performing some action. In this case, an attacker, or attackers, are attempting to manipulate victims (targets) into taking a USB device and plugging it into their computer. Depending the type of USB drop attack, an attacker(s) may further manipulate victims into clicking on files loaded onto the USB device.
This type of attack has been used for years by everyone from lowly “script kiddies” all the way to nation-state hacking groups. The reason it is seen so much is because it can be effective and difficult to defend against. Depending on how this attack is deployed, it can be targeted to a single individual or organization or randomly distributed. A famous example of this attack is the Stuxnet worm. Stuxnet was a malicious worm designed to destroy centrifuges used in SCADA system at specific nuclear plant in Iran. The attack was thought to have been distributed via USB devices due to the SCADA system being disconnected from the internet for security reasons. This worm had several versions found, some versions exploited several zero-day vulnerabilities, including in the centrifuges’ program on Windows machines. It destroyed approximately a fifth of the centrifuges within the plant. It has been thought that the worm was developed and distributed jointly by the United States and Israel, although both countries have denied this.
Why are these Attacks Effective?
The reason this attack can be so effective is because it uses humans’ natural curiosity and/or desire to help others against them. When there is a device laying around that has potentially “juicy” information on it, humans cannot help themselves but to take these devices and see what’s inside. An effective attacker leverages humans’ innate curiosity to get a victim to take a USB device. Once a device is taken, the odds are good that the contents will be examined by the victim. However, many skilled attackers will not simply hope that victims will click the right file. Attackers will add enticing files or file name within the device to further play on those human traits that made them pick up the device in the first place. Even when people are trained to spot these attacks, they can still fall for them because it can be so enticing.
However, not all of the blame can be given to humans. The machines these devices get plugged into don’t do much checking either. Some devices with Windows OS simply ask what you want to do with the device. Once a file is clicked, it is up to the machines’ firewall and installed antivirus to stop anything malicious. You can do a malware scan once the device is inserted, but often times that requires forethought of the human controlling the machine. There are few adequate countermeasures that machines take to stop strange USB devices that get inserted.
Types of USB Drop Attacks
USB Human Interface Device (HID) Spoofing:
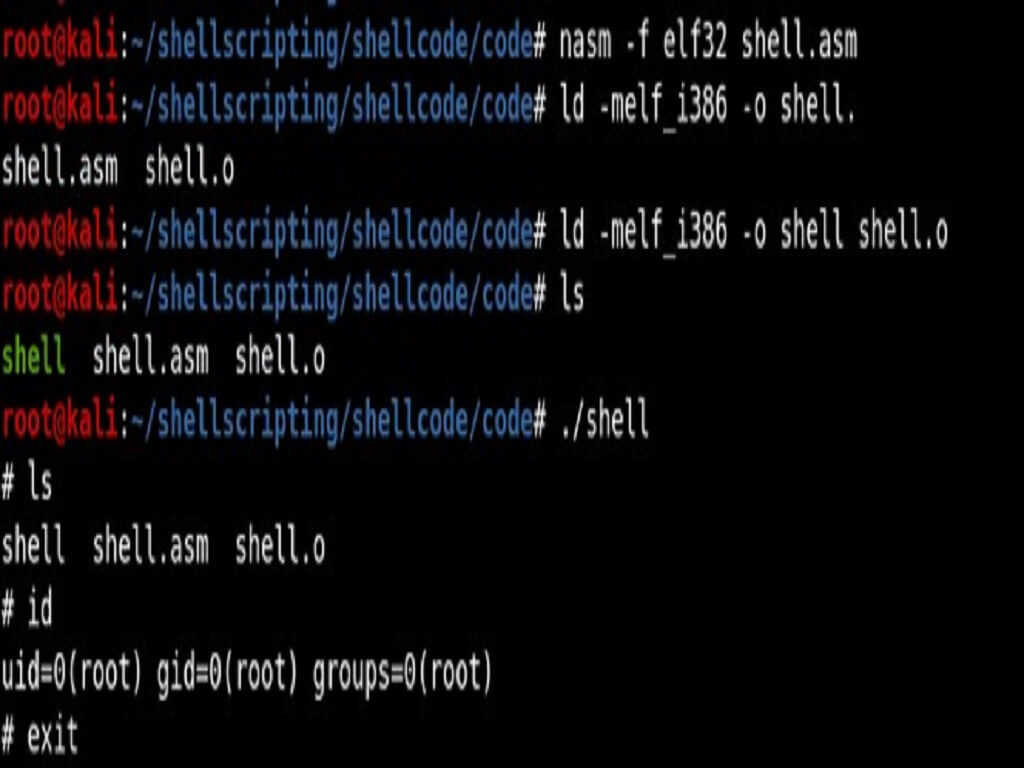
Before talking about USB Human Interface Device (HID) spoofing, first we need to understand what human interface devices are. HIDs are devices that attach to computers via the USB port, or similar ports, that allows humans to input data or allows machines to provide output to humans. Examples of HID devices include: keyboards, mice, headphones, microphone, etc. HID spoofing, in terms of a USB drop attack, tricks a machine into thinking a keyboard is in use by a human. When this device is plugged into a machine, it can then execute pre-programmed keystroke on the machine.
This type of USB drop attack is very versatile because it can be used across different operating system platforms including Windows, MacOS, and Linux. This attack cannot be used with every USB device but instead requires specific microcontrollers that support keyboard emulation. A microcontroller is essentially a tiny computer on a single integrated chip. There are a few different HID devices that can be purchased and used after some setup. Two of the most popular devices are the USB Rubber Ducky from Hak5 and the Malduino by Miltonic’s. HID spoofing devices can also be made from Arduino boards that are close to the size of a typical flash drive. However, these devices require additional programming and hardware setup to get these devices to look like typical flash drives. There are also a small number of certain flash drives that can be converted into HID devices with some programming. These devices use its own programming language called Ducky Script. Ducky Script is a simple scripting language that can emulate anything a keyboard can do.
There are some drawbacks to using this type of device in a USB drop attack. Since this device injects keystrokes, it may be possible for the victim to notice this if they are not properly hidden and unplug the devices before completion. These devices must be plugged into the target device for a predetermined time in order for the attack to be successful. If an alert victim notices keystrokes or becomes inpatient that no storage is becoming visible after plugging it in, it may be removed before the payload completes. This is why it is so important when an attacker uses this device in an attack to make payloads that are not visible or briefly visible and completes quickly.
Malicious Files/Code:
Another type of USB drop attack is the use of malicious files loaded onto an everyday flash drive. Once a victim opens a file containing the malicious code, the code activates. What these malicious files can do is virtually endless, including downloading other malicious files from the internet. These attackers are only limited by the attacker’s imagination and the machine’s countermeasures such as antivirus.
Files Used in these attacks are usually given enticing names to get victims to click on them. A very popular way to get people to click on malicious files is to play on victims’ lust by placing potentially pornographic pictures on the flash drive. Attackers with less experience may not know how to disguise files and depend on victims clicking them despite the obvious danger. More experienced attackers find ways to disguise these files and make it harder to spot the danger. For example, a malicious file can be hidden inside another file, such as an exe file being placed inside a picture. This technique is known as steganography
The advantage of using this version of attack versus HID spoofing is the code can run entirely hidden from view if executed properly. Sometimes victims will have no idea there was an attack if the code ran circumvents the malware protection on the machine. Another advantage is this attack can be performed on any flash drive with enough storage. This allows attackers quick and easy access to more accessible devices. A disadvantage of this attack is that some malicious files can be stopped by the machine’s countermeasures like antivirus.
Social Engineering Links:
This attack involves the use of malicious phishing links. In this attack, an attacker places website links on the flash drive that directs the user to a phishing site or to malware. Typically, these malicious links will direct users to websites set up by the attacker that attempt to harvest the victim’s credentials, attempt to extort victims, download malicious files, or other attacks. These phishing sites can masquerade as other sites such as email hosting sites like Gmail, Yahoo, and others to trick users to input their credentials. Although this attack can be used with HID spoofing devices by taking a victim to a phishing site with the keystroke commands, it is more likely to be used on an everyday flash drive. There are a few disadvantages of this attack. This attack is dependent on internet access and requires the victim's computer to be connected to the internet. If the victim is not connected to the internet, the attack will fail. This attack sometimes relies more heavily on the use of social engineering to trick gullible users into clicking links and then performing the desired action on the phishing website
USB Kill:
This attack is the most destructive out of all USB drop attacks. When plugged in, the USB Kill creates a power surge destroying the machine. The vast majority of devices are not protected against this type of attack. USB ports in machines have two functions, the power the USB devices and communicate with USB devices. What the USB kill does is it takes the power from the machine’s USB power lines and stores the voltage. Once the voltage reaches a certain point the devices then discharges that stored power through the USB data lines. The device will do this continuously until the machine is destroyed or until it is unplugged. They have a few different versions with adapters (Micro USB, USB-C, Lightning) to attach to other types of devices like smartphones. Some come with an easy to spot emblem. However, some of these devices are hard to spot because they sell an “anonymous” edition that has no markings to indicate it is a USB Kill.
Zero Day:
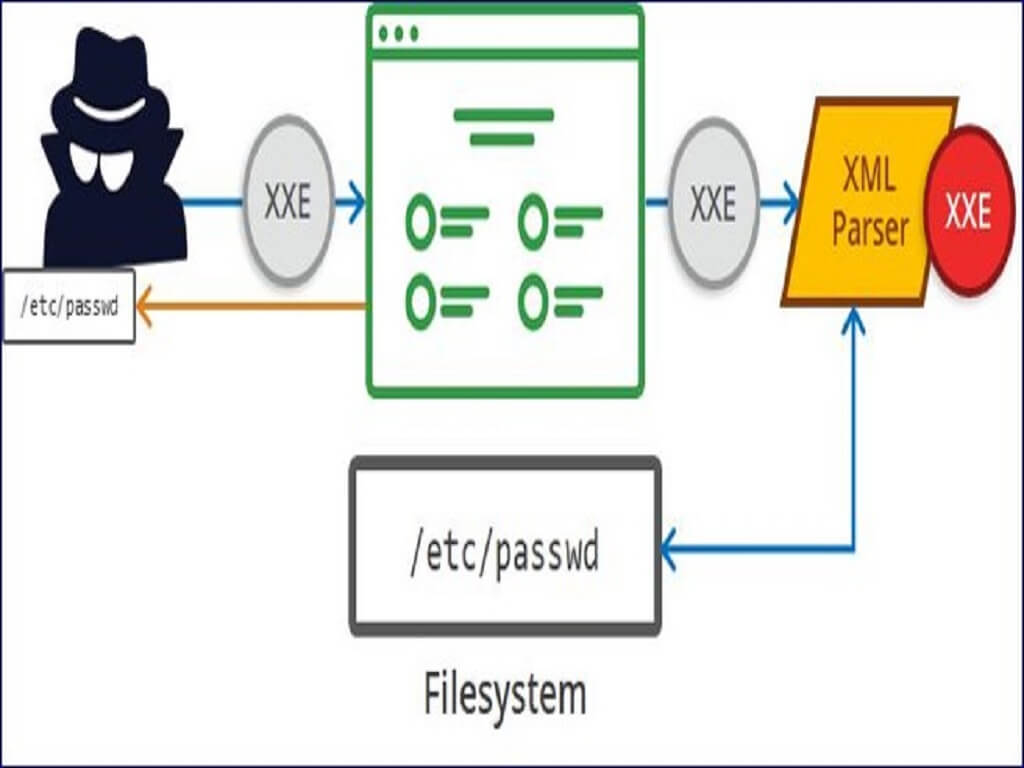
This attack takes advantage of an undiscovered vulnerability in the machine’s software. When this category of attack is talked about, it almost always references the Stuxnet attack. Stuxnet was a rare example that used several zero-day vulnerabilities in its targeted attack. Many cyber security experts will also call this a Zero Day Driver attack. This is because when machines have external devices connected the driver software is installed, and there exists the possibility of having malicious code attached to that driver software. Some cyber security experts do not include this attack as its own category but instead place it with the malicious file/code category.
The logic of categorizing it appears to exist both ways making it the most ill-defined category of USB drop attacks